Zuse Z3 at the Deutsches Museum

The Z3 by Konrad Zuse was the world’s first working digital Turing-complete computer. It did floating point arithmetic, had two registers accessible to the programmer, was microcoded, and clocked at about 5 Hz.
Archimedes Operating System (PDF)
Amiga & Supergrips

This article is in German, since it is about the German TV show “Supergrips” and how the scoreboard was implemented.
The Ultimate Commodore 64 Talk: Pushing Keynote to its Limits
Download the Apple Keynote 08 presentation.
The Ultimate Commodore 64 Talk @25C3
Update: Video recording available.
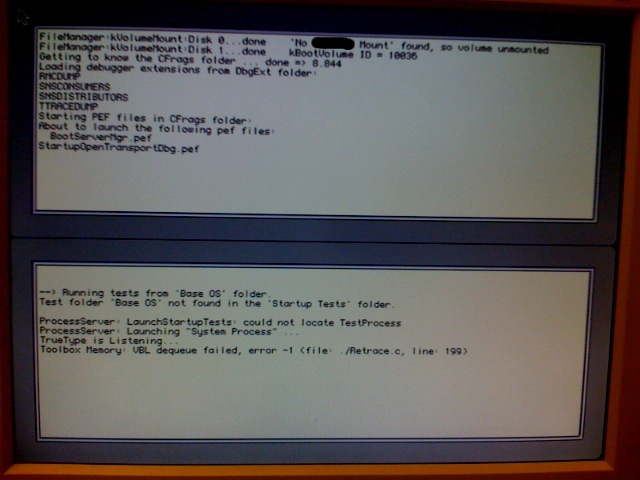
Copland D9 Booting
What Operating System Is This?
Inside Macintosh Volumes I, II, III (PDF)

Here are all three volumes of the original 1985 edition of Inside Macintosh as a searchable PDF:
Reconstructing the Leftovers on the Amiga Kickstart 1.0 Disk
Update: The source is available at github.com/mist64/extract-adf; more info here.
64'er 04/1984 (PDF)
I converted the first issue of the German Commodore 64 magazine 64’er into a searchable PDF:
Commodore BASIC as a Scripting Language for UNIX and Windows – now Open Source
Update: The source is available at github.com/mist64/cbmbasic
Transactor November 1987: Volume 8, Issue 3 (PDF)
The other day, I found this at WeirdStuff:
Create your own Version of Microsoft BASIC for 6502
Update: The source is available at github.com/mist64/msbasic
"ROR" in Microsoft BASIC for 6502
If you disassemble any version of Microsoft BASIC for 6502, you’ll find this code in a function that normalizes the (simulated) floating point accumulator:
Building the Solaris Kernel in 73 Easy Steps
Everyone and their grandmother builds Linux kernels. Many people build BSD, and some brave men even compile the OS X kernel every now and then. Why not compile your own Solaris kernel for a change?
Bill Gates' Personal Easter Eggs in 8 Bit BASIC
If you type “WAIT6502,1” into a Commodore PET with BASIC V2 (1979), it will show the string “MICROSOFT!” at the top left corner of the screen. Legend has it Bill Gates himself inserted this easter egg “after he had had an argument with Commodore founder Jack Tramiel”, “just in case Commodore ever tried to claim that the code wasn’t from Microsoft”.
The Xbox 360 Security System and its Weaknesses
After the disaster of the original Xbox, Microsoft put a lot of effort in designing what is probably the most sophisticated consumer hardware security system to date. We present its design, its implementation, its weaknesses, how it was hacked, and how to do it better next time.
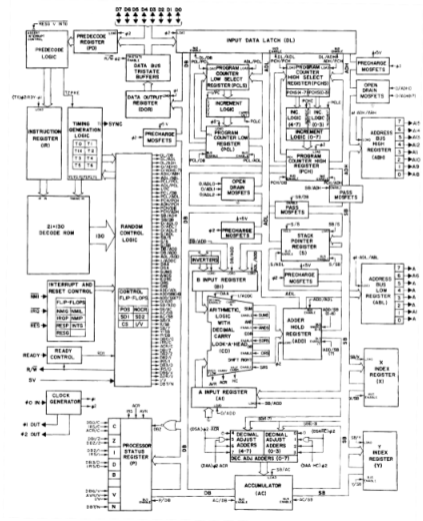
How MOS 6502 Illegal Opcodes really work
The original NMOS version of the MOS 6502, used in computers like the Commodore 64, the Apple II and the Nintendo Entertainment System (NES), is well-known for its illegal opcodes: Out of 256 possible opcodes, 151 are defined by the architecture, but many of the remaining 105 undefined opcodes do useful things.