Das Statistikbuch zum Commodore 64 [PDF]
Werner Voß:
Das Statistikbuch zum Commodore 64
Düsseldorf: Data Becker, 1985.
ISBN 3-89011-102-5.
(468 pages, 33 MB)
Danke an Dirk Wagner für die Bereitstellung des Buchs.
Das Schulbuch zum Commodore 64 [PDF]

Werner Voß:
Das Schulbuch zum Commodore 64
Düsseldorf: Data Becker, 1984.
ISBN 3-89011-019-3.
(354 pages, 21 MB)
Danke an Dirk Wagner für die Bereitstellung des Buchs.
Das Grafikbuch zum Commodore 64 [PDF]

Axel Plenge:
Das Grafikbuch zum Commodore 64
Düsseldorf: Data Becker, 1984.
ISBN 3-89011-009-6.
(305 pages, 28 MB)
Danke an Dirk Wagner für die Bereitstellung des Buchs.
Das Commodore-64-Spiele-Buch [PDF]
Owen Bishop:
Das Commodore-64-Spiele-Buch
Frankfurt/M.: Commodore, 1984. (Commodore-Sachbuchreihe, Bd. 4)
ISBN 3-89133-002-2.
(162 pages, 29 MB)
Aus dem Englischen übertragen von Gudrun Breiter. Originaltitel: The Commodore 64 Games Book – 21 Sensational Games (Granada Publishing, 1983).
Danke an Dirk Wagner für die Bereitstellung des Buchs.
Das Nikolaus-Heusler-Archiv
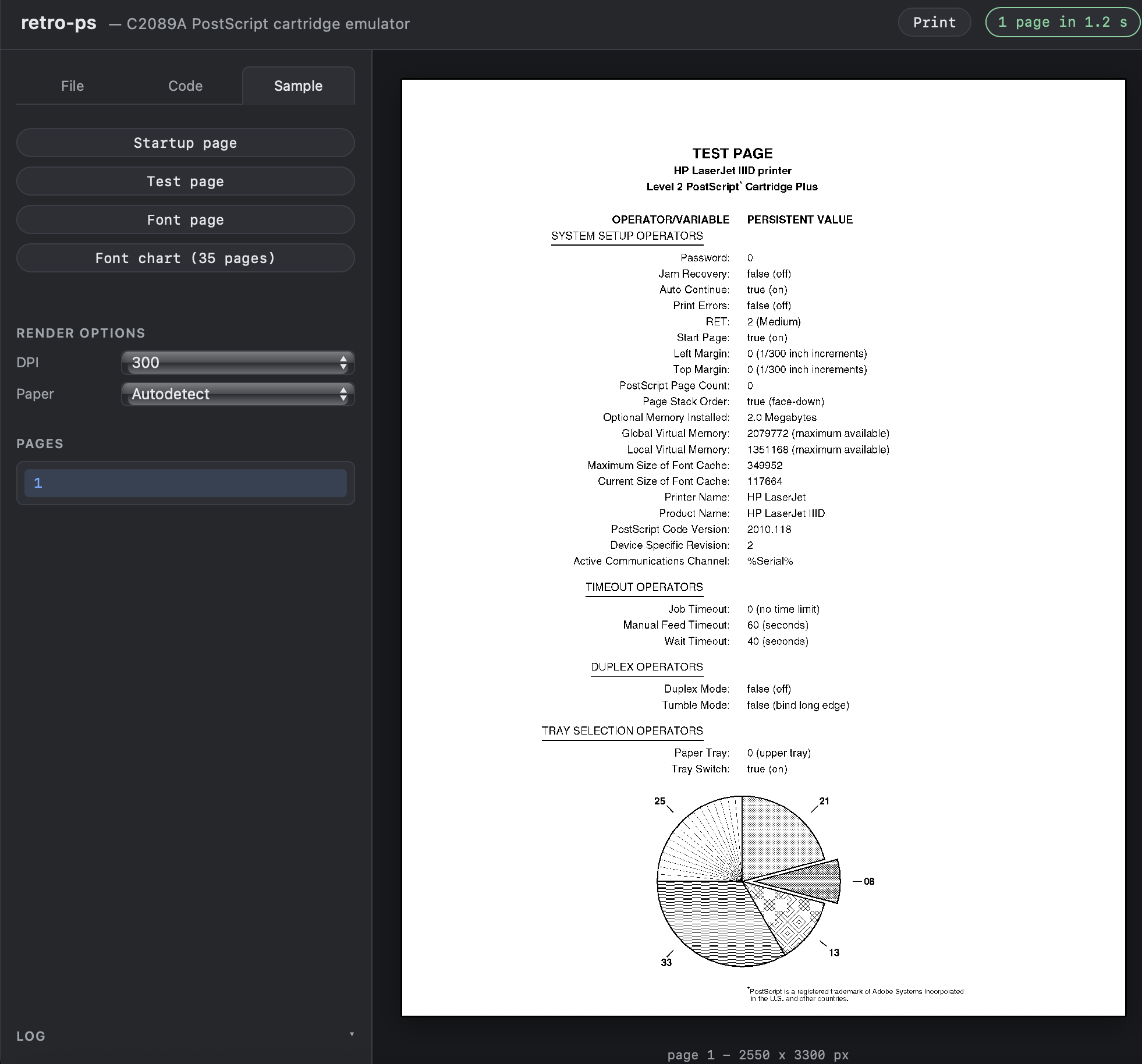
Running Adobe’s 1991 PostScript Interpreter in the Browser
The HP C2089A “PostScript Cartridge Plus”, a 1991 add-on for the LaserJet II/III, adds PostScript Level 2 support through Adobe’s own reference interpreter (version 2010.118) on a 2 MB ROM.
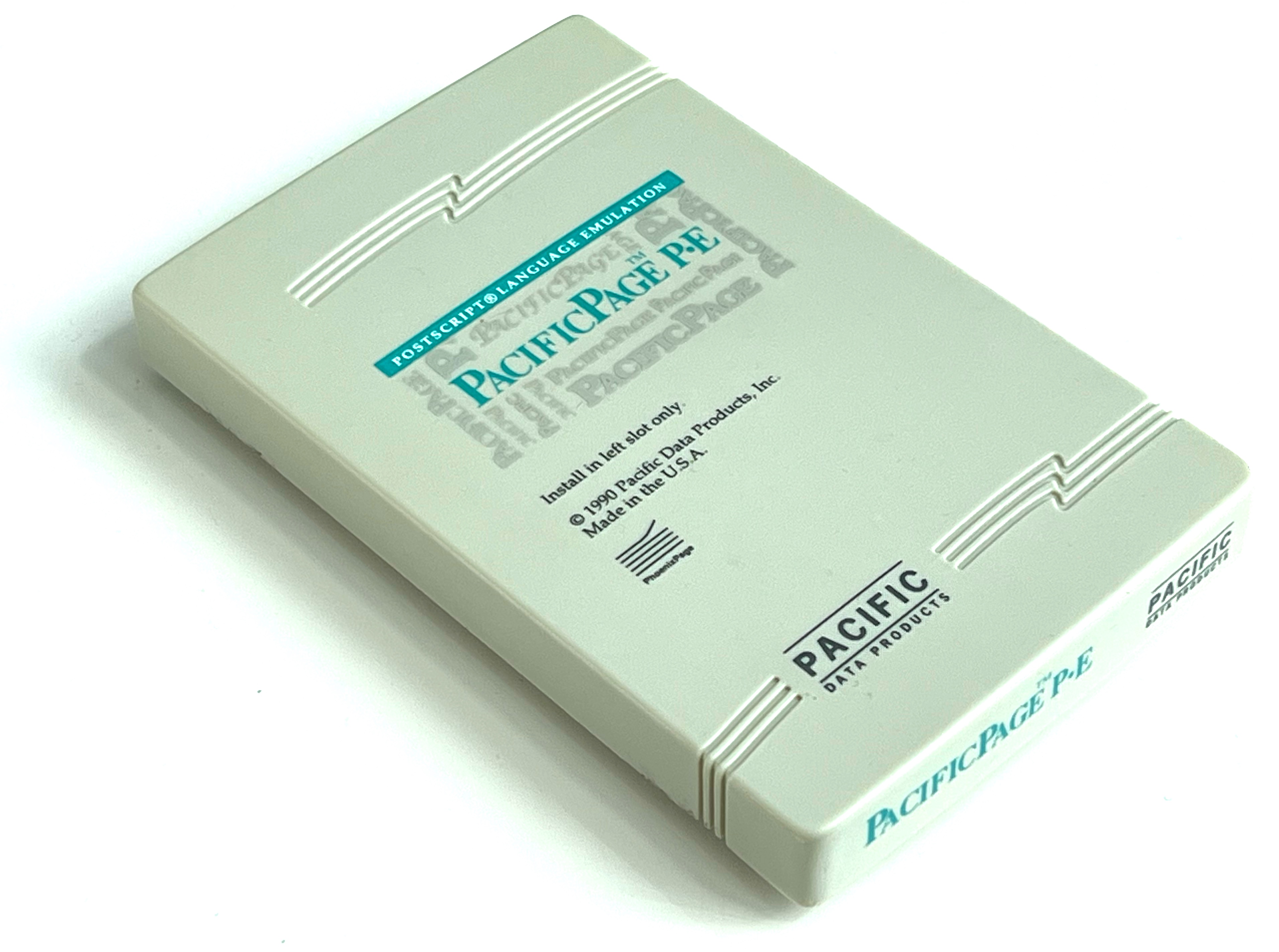
PacificPage P·E PostScript Cartridge for HP LaserJet II/III
Lohnsteuerjahresausgleich? Einkommensteuererklärung? Mein C 64 hilft mir dabei! [PDF]

Ilona Kwiatkowski, Peter Vogt:
Lohnsteuerjahresausgleich? Einkommensteuererklärung? Mein C 64 hilft mir dabei!
Heidelberg: Hüthig, 1985.
(204 pages, 16 MB)
Danke an Dirk Wagner für die Bereitstellung des Buchs.
Einführung in CAD mit dem Commodore 64 [PDF]
Werner Heift:
Einführung in CAD mit dem Commodore 64
Düsseldorf: Data Becker, 1985.
ISBN 3-89011-067-3.
(322 pages, 18 MB)
Danke an Dirk Wagner für die Bereitstellung des Buchs.
Das große Drucker-Buch [PDF]
Rolf Brückmann, Klaus Gerits, Thomas Wiens:
Das große Drucker-Buch
Düsseldorf: Data Becker, 1984.
ISBN 3-89011-020-7.
(392 pages, 26 MB)
Danke an Dirk Wagner für die Bereitstellung des Buchs.
Klaus Finke’s Commodore 64/128 GEOS Disk Collection
This is a collection of 111 Commodore 64/128 disk images from a box of CMD FD-2000 high-density floppy disks. The disks came from the estate of Klaus Finke (1945–2016), a GEOS community organizer from Suhl, Thuringia.
How the Final Cartridge III Freezer works
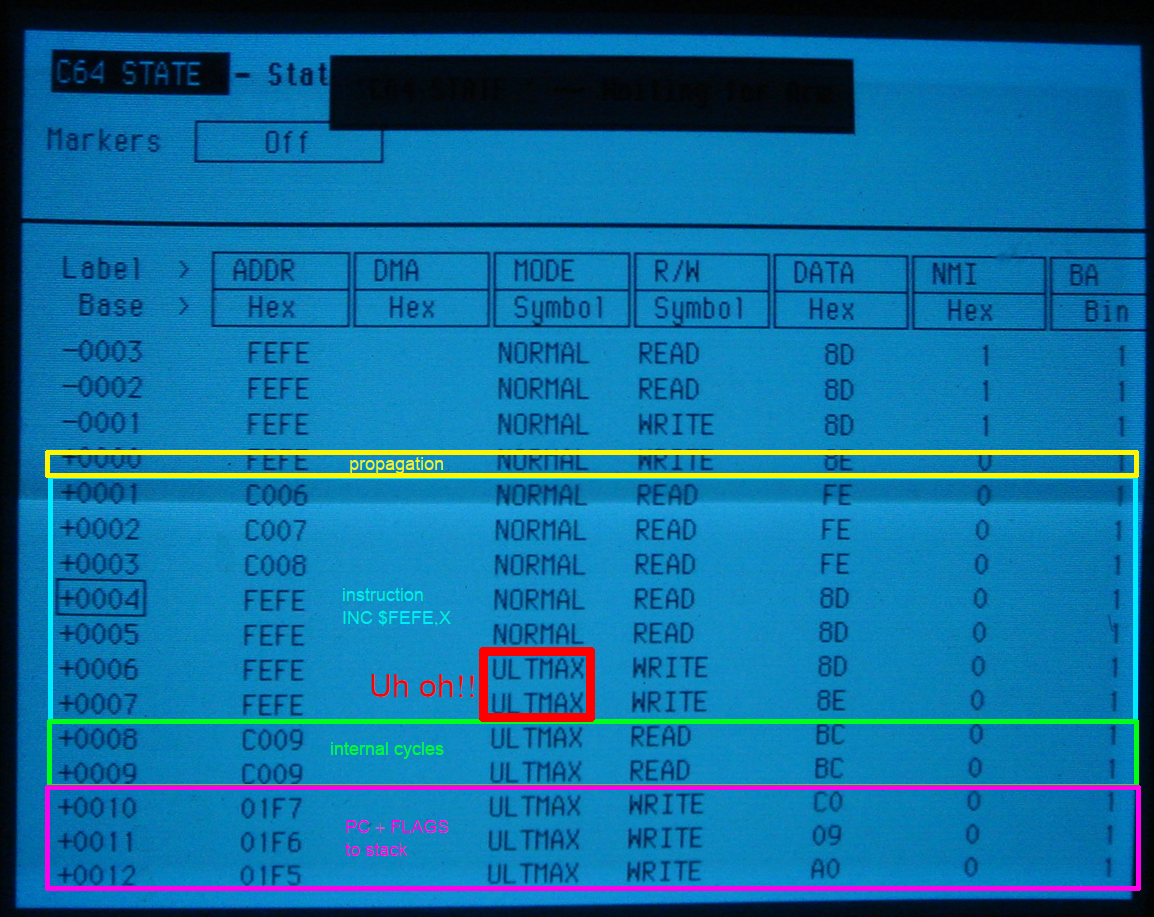
by Daniël Mantione
64 Tips & Tricks [PDF]

Michael Angerhausen, Lothar Englisch, Klaus Gerits, Frank Thrun:
64 Tips & Tricks
Düsseldorf: Data Becker, 1984. (4. erweiterte und überarbeitete Auflage)
ISBN 3-89011-001-0.
(386 pages, 26 MB)
Danke an Dirk Wagner für die Bereitstellung des Buchs.
6502 Illegal Opcodes in the Siemens PC 100 Assembly Manual (1980)
The 6502’s “illegal” opcodes were of intense interest to home computer enthusiasts, and analyses were published in various magazines. But one would have never expected a company like Siemens to document illegal opcodes in a programming manual from 1980.
Siemens Personal Computer PC 100 Bedienungsanleitung, Ausgabe 1981/1982
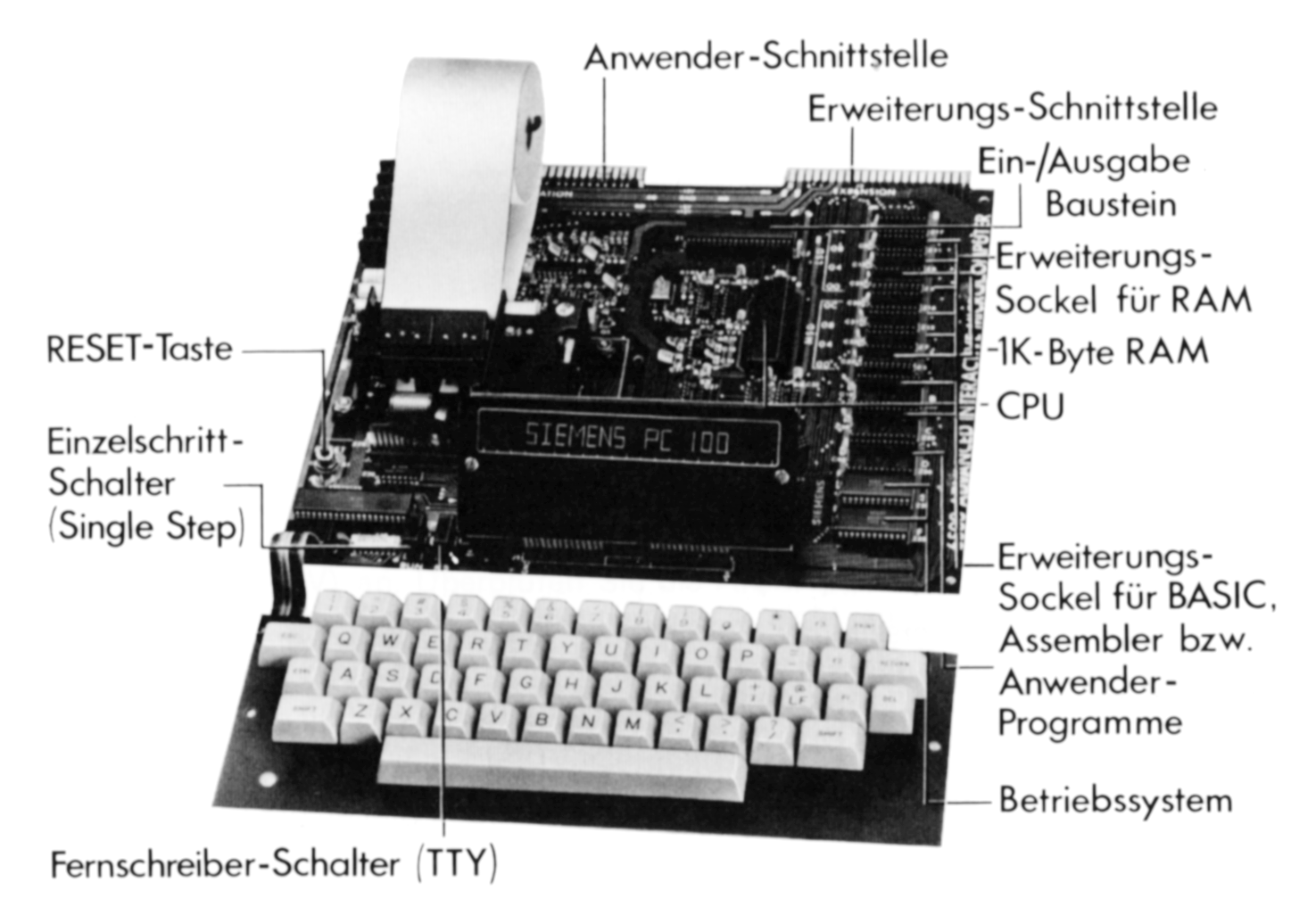
The Siemens PC 100 was a version of the 6502-based “AIM-65” SBC in a case and with slightly modified ROMs. Siemens offered a set of German-language manuals, which included translated Assembler (MOS Resident Assembler) and BASIC (Microsoft BASIC) manuals, but also a general manual (“Bedienungsanleitung”).
Brotkastenfreunde Interview
In Folge 017 des C64-Podcasts Brotkastenfreunde bin ich diesmal Gast.
Das Titelbild vom 64’er Sonderheft 2/85

Am 25. März 1985 kam das zweite 64’er Sonderheft mit dem Thema Abenteuerspiele raus. Genau 40 Jahre später ist es nun als HTML und PDF online verfügbar – im Kontext des Projekts 64er-magazin.de. Der Drachenreiter auf dem Original-Titelblatt ist der damals 18jährige Boris Schneider-Johne – wer genau schaut, wird auf der Website erkennen, dass wir das Bild aktualisiert haben:
64'er Magazin – mit 40 Jahren Verzögerung jetzt monatlich im Web

Zum 40jährigen Jubiläum des 64’er Magazins präsentieren wir das Kunstprojekt www.64er-magazin.de: eine Website, die so tut, als wäre 1984. Exakt 40 Jahre nach der ursprünglichen Veröffentlichung erscheint hier jeden Monat eine neue Ausgabe:
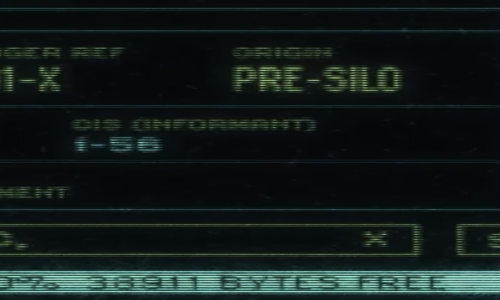
Silo S01E06: 38911 BYTES FREE
[Ankündigung] Vortrag “Apollo Guidance Computer” an der Embedded Computing Conference in Winterthur
This post is about an upcoming talk in German.